When I think of the term “sextortion” I think of an offense marked by deceit, manipulation, and the callous exploitation of human vulnerability. I think of trust being violated, and I think of absolute heartbreak from the fallout. Finally, I think of wounds from which it seems very hard to recover. It also reminds me of the phenomenon of Revenge Porn, which is more related to public humiliation while sextortion is marked by private control and the abuse of power stemming from unauthorized possession of a personal image or video. Some might even consider it a form of electronic sexual assault.
Here at the Cyberbullying Research Center, targets of online victimization frequently reach out to us for help. And while I don’t have clear trend data on this, anecdotal evidence shows me that specific cases of sextortion are on the rise. As recently as today, I received the following request for assistance:
I did something bad. girl send me nude and i send back also and she looks’ kinda nice person first. then she screenshoted my instagram followers and she said that she will send my nudes for all my followers! PLS HELP! My account is ******* and her is ****** . IF she send i’ll be dead. i guess so. my family will see and all my friends and people that i know.
Justin will attest to the fact that more and more of these type of pleas are coming in. And this phenomenon needs to be studied in detail.
Thankfully, the University of New Hampshire Crimes Against Children Research Center and our colleagues Janis Wolak and David Finkelhor partnered with a nonprofit organization called Thorn to explore sextortion, and just released a detailed report of their findings. I found the inquiry riveting, and wanted to summarize for you some of the most important findings.
First, though, I want to point out that this exploratory study involving 1,631 persons ages 18-25 used a purposive sampling method. That means that they intentionally sought out victims of sextortion through Facebook and Twitter ads, who then clicked through to participate in an anonymous survey online. The researchers also aimed to make sure they came from a variety of demographics (LGBTQ, racial and ethnic minorities, etc.) by targeting ads to those specific populations. The point here is that these findings CANNOT be generalized outside of this select group of survey respondents and we don’t have an idea of how often this occurs in the general population. The authors make this clear, and are simply reporting the experiences of the sextortion victims who participated in the research.
Now to the interesting take-home points:
The researchers state that sextortion involves threats to expose a sexual image in order to make a person do something or for other reasons, such as revenge or humiliation. I like this definition as it is broad. Other definitions we have seen are overly restrictive, and state that the sexual image is used only to extort additional sexual content or sexual activity. While the perpetrator typically is interested in that end game, we’ve also seen cases where the goal was a monetary payment, ruining a reputation, or to get the target to do something else s/he wouldn’t normally do.
With regard to gender, respondents were made up of women (83%), men (14%), and those who selected the choice of “Other” (2%).
Almost half (46%) were minors (17 years of age or younger) when the sextortion began.
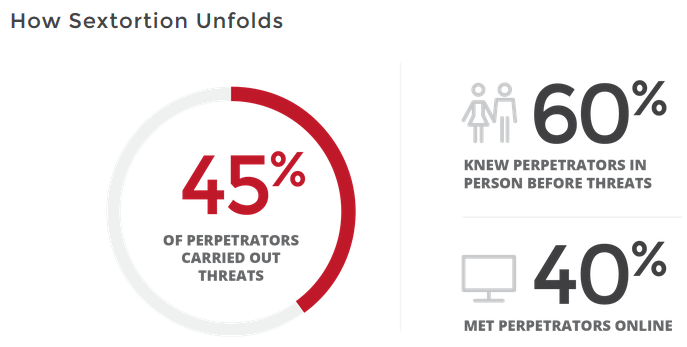
A notable 3 out of 5 (60%) knew the perpetrator in real life prior to the victimization, while 40% met them online. Said another way, most cases involved a real-world romantic relationship where pictures or videos were taken, and then one partner used it to manipulate or humiliate the other. The rest of the cases involved an interaction online which eventually resulted in a personal image sent or received being used to demand further sexual content, activity, or something else of value.
Contact between perpetrators and victims happened across many mediums: social networks (54%), messaging apps (41%), video voice call apps (23%), email (12%), dating apps (9%), and even gaming platforms (4%). In almost half of the victimizations (45%), multiple platforms were employed.
In the interactions which began online, the respondent indicated that the perpetrator lied about who they were or otherwise gave a false impression in 55% of the cases. The lies were about wanting a romantic relationship (42% of those who lied), their age (39%), their gender (17%), being someone they knew (13%), or something else (21%).
About 70% in both face-to-face and online relationships knowingly provided a sexual image to the perpetrator. The reasons were because: they were in the relationship (72%); they felt pressured or made to feel bad (51%), they were tricked (15%), they were threatened or forced (13%), they expected to be paid for them (2%), or they thought the images would be used for modeling or acting (2%). Overall, 40% provided the image freely to maintain the relationship, because they liked the other person, or because they didn’t think it was a big deal.
In 45% of cases, images were acquired by the perpetrators without the knowledge or consent of the target. In 18% of cases, webcam images were recorded. In 9%, they were taken without permission from a mobile phone. In 8%, they were fake or Photoshopped. Finally, in 5% they were accessed by hacking into the computer or mobile device of the target.
In my mind, absolutely the most intriguing aspect of this research project was the inquiry into what perpetrators wanted from their targets. The percentages were as follows:
- Additional sexual photographs or videos from the respondent – 51% of all respondents
- For the respondent to stay in or return to a relationship with the perpetrator – 42%
- To tell the respondent how to look or what to do in pictures or videos – 28%
- To meet the respondent in person (usually for sexual activity) – 26%
- To meet the respondent online for sexual activity – 24%
- To tell the respondent to hurt themselves – 10%
- To blackmail the respondent for money – 9%
- To make the respondent take sexual images of someone else – 7%
Similarly fascinating (and downright scary) was what the perpetrators actually did to carry out their threats. This happened in close to half (44%) of cases in the following ways among those who revealed that threats were carried out:
- Stalked respondents with repeated, unwanted online or cell phone contact – 71%
- Sent sexual images depicting the respondent to people the respondent knew – 45%
- Posted sexual images online – 40%
- Posted personal information about the respondent with such images – 26%
- Hacked into online accounts that belonged to the respondent – 24%
- Created fake web pages or accounts that appeared to belong to respondents or fake photos that appeared to portray them – 15%
- Offline, threats were also carried out in the following ways:
- Stalked or harassed respondents in person or tried to – 41% of those who said that perpetrators carried out threats
- Got them in trouble at work or school or with the law or tried to – 37%
- Beat, raped or physically hurt them or tried to – 33%
- Harmed family, friends or pets or tried to – 12%
- Extorted money or tried to – 11%
Here’s another request for help our Center received the other day:
hey im a ** year old girl from ********. I have been cyber bullied by my ex-bf. He spreading my nudes and it affects my study and my career. He also contact my parents and intended to spread my nudes at their workplace. So me, as their child, they feel so guilty. I feel like i want to kill myself. I cant find him because he already fled to ********. And using fake email account to threaten my parents.
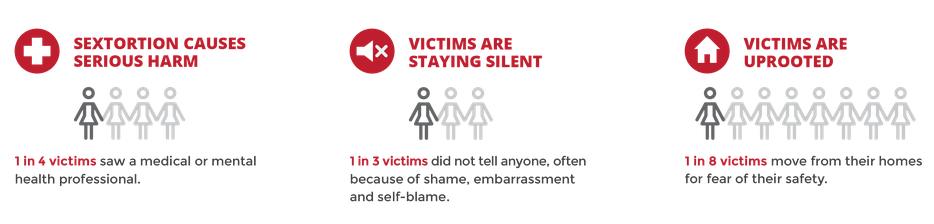
When victimized, targets felt quite helpless – and perhaps understandably so. Almost half (45%) felt uncomfortable or unable to confide in family or friends about what happened. This largely stemmed from feelings of shame, embarrassment, fear of retribution, or a sense that it simply wouldn’t do any good. Relatedly, only 21% reported the situation to the relevant website or app, and only 16% reached out to the police. It is sad to say that many who contacted law enforcement received negative or dismissive responses. As we know from the domestic violence literature, this can rightly be conceived a double victimization, where the very people to whom you contact for help don’t seem to care. Overall, one in three victims did not tell anyone else (until reporting it anonymously in this survey).
In terms of harm, sextortion is taking a terrific toll on victims. 27% of victims in face-to-face incidents and 21% in online incidents sought professional mental or medical help following their experience, while 16% in face to face and 5% in online incidents moved away from their homes for fear of their safety. Relatedly, 14% in face-to-face and 5% in online incidents had school problems, while 11% in face-to-face and 4% in online incidents experienced job problems.
As is evident, our colleagues at the University of New Hampshire Crimes Against Children Research Center made some important discoveries through their quite thorough analysis of sextortion. Before wrapping up here with some final thoughts, I quickly want to provide a bit of context in the form of supporting research in this area. In May 2016, the Brookings Institute released a study of 78 prosecuted cases involving 1,397 known (and thousands more unknown) victims of sextortion. Here, they reported similarly alarming findings and highlighted a few critical trends. Every single prosecuted perpetrator was male, and often a repeat offender. To note, 25 cases involved at least 10 victims, 13 involved at least 20 victims, and 13 others involved more than 100 victims. Most cases (71%) only involved victims under the age of 18, and while most were female there were some instances of minor boys being victimized. In this particular study, they found that social media manipulation was involved in the vast, vast majority of situations (91%), while hacking of targets’ computers or other devices of the targets occurred in 43% of in cases.
Finally, the US Department of Justice released a report in April 2016 entitled “The National Strategy for Child Exploitation Prevention and Interdiction” which further underscored the weight and significance of this problem. They confirmed that sextortion is on the rise – “by far the most significantly growing threat to children” and that “sextortion cases tend to have more minor victims per offender than all other child sexual exploitation offenses.” They also referenced an FBI analysis of 43 sextortion cases in 2015, and point out that 28% had at least one child victim who attempted or completed suicide – testifying to the very grave potential consequences of victimization.
In closing, these studies paint a very grim picture of an increasingly concerning form of online cruelty. All emphasize the fact that most sextortion is motivated by pure malice and the desire to humiliate the target. They also point out that there aren’t clear pathways to follow once victimized to improve the situation or achieve justice. Wolak and Finkelhor assert that once the images are in the hands of a motivated aggressor, the target can’t do much – and that even if they reach out to a website or app, those “companies’ procedures for evaluating content did not always give consideration to the wishes of persons depicted in images or take into account their embarrassment and emotional distress.” Most of the time, sextortion occurred within a constellation of other crimes, like dating violence, stalking, and harassment. And, as mentioned earlier, law enforcement appears impotent or uninterested to help – at least based on the respondents in this survey.
Where do we go from here? I will tackle this in a future blog when we share our own findings on the problem of sextortion, but we have to move past generalities and into specifics. The standard lines involve “raising awareness” and getting professionals to care more (perhaps passing clear federal laws with strong penalties, and getting law enforcement to do more to help victims). I get that. Those are important. But more is required. What should the primary messages be to everyone out there?
- Verify via FaceTime or Skype who you are talking with?
- Get and verify their identity and address before the conversation turns sexual, so you have something on them just in case?
- Don’t send vulnerable pictures or videos because you can’t trust anyone?
- Practice better internet security so your devices don’t get hacked?
- Don’t keep anything sexy on your camera roll?
- Stop caring if your nude pictures are out there, because then no one can hold them against you?
Like the other issues we face at our Center (cyberbullying, sexting, digital dating abuse, etc.), complexities abound. We have to dig deeper to figure out exactly what will work, so we know exactly what to do.
Image sources:
http://storage.ottawasun.com/v1/dynamic_resize/sws_path/suns-prod-images/1297606157104_ORIGINAL.jpg?quality=80&size=420x
https://www.wearethorn.org/wp-content/uploads/2016/06/thorn_sextortion_1.png
https://www.wearethorn.org/wp-content/uploads/2016/06/sextortion-text-thread.jpeg
https://mic.com/articles/143200/these-7-devastating-statistics-show-why-we-need-to-make-sextortion-illegal-right-now
https://cbsdenver.files.wordpress.com/2015/09/cu-sextortion-10pkg-tran6sfer.jpg?w=1500https://images.mic.com/3oikhstix599r9ahnizskdrjg1xij1dvmq83oadddjd3u164phpzdcvm0ihvrbrh.jpg







Really good job here guys.
before u post think once u post it u cant return it back
Why are there so many good articles about this but NO ONE says how to get it to stop??!! I have contacted the local and state police, who just spoke condescendingly to me, and minimized the severity of the situation. I also attempted to contact the FBI and Interpol, with no response.